It is fascinating how the term Extended Detection and Response (XDR) holds varying interpretations in the cybersecurity industry. Conversations with leading analysts, IT leaders, C-suite executives and other stakeholders often reveal distinct perspectives on XDR. Regardless of everyone’s definition of XDR, one thing is undeniable though, XDR has the potential to become the most significant cybersecurity category to date.
At its essence, XDR harnesses data and sensors to augment threat detection and response capabilities. But the true strength of XDR lies in its capacity to automate processes, efficiently examine alerts, and proactively respond, particularly to high-priority alerts and threats.

This blog delves into the evolving realm of cybersecurity, with a specific focus on Extended Detection and Response (XDR). It will also explore how XDR compares to its predecessor, Endpoint Detection and Response (EDR).
The Rise of Endpoint Detection and Response (EDR)
Let’s begin our exploration by looking at EDR, which has played a pivotal role in early malware detection. EDR, or Endpoint Detection and Response, is a cybersecurity solution that offers a level of protection that outshines traditional antivirus software solutions.
EDR acts as a vigilant guardian of your employee endpoint devices, which include computers, laptops, tablets and smartphones etc. The aim is to continuously monitor these endpoints to detect any suspicious activities that might signal a lurking threat. Once any such threat is identified, EDR does not waste a moment and responds with agility, cutting off the threat.
Remember, the beauty of EDR lies in its laser sharp focus on securing endpoint devices. The way this niche expertise empowers businesses to protect their endpoints, and identify advanced threats that often slip through the cracks, is truly incredible.
And while EDR is an extremely potent tool, it is important to note that it is designed to safeguard only one facet of your IT infrastructure – the endpoints. Basically, it is not an all-encompassing solution that caters to every aspect of your cybersecurity needs.
The XDR Revolution is Upon US
This brings us to the next stage of evolution – Extended Detection and Response or XDR. It is like the upgraded version of EDR, taking everything you knew about endpoint protection, and “turning it up many notches”. It is not just about looking after your regular endpoints anymore; XDR casts its watchful eye over a diverse array of platforms and technologies, across your IT infrastructure and environment.
The Cloud plays a significant role in the increasing popularity of XDR. We say that because in the past, EDR did a good job of keeping our physical devices safe from cyber threats. But now, with the Cloud in the picture, things have changed. In the XDR world, an “endpoint” isn’t just a physical device anymore. Rather, it is the final destination for all our digital communication, processes and workloads. Most of our important data now lives in the Cloud.
Moving from EDR to XDR means adapting to this shift, and using new sources of information to enhance the overall cybersecurity posture. As many critical business operations now happen in the Cloud, XDR is all about keeping that space secure.
The Compelling Benefits of XDR
Market analysis and reliable research tells us that businesses that have embraced XDR are also seeing tangible results in their operations. They have slashed the time it takes to detect and resolve security breaches, making life a lot harder for cyber miscreants.
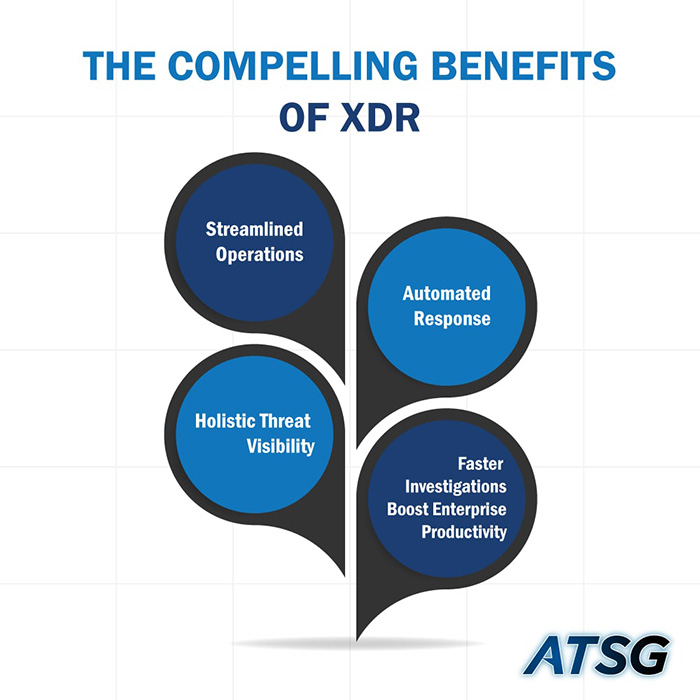
Considering these facts, all the buzz around XDR is well-founded. In the following points, we highlight some other benefits of XDR.
1. Streamlined Operations
First off, XDR simplifies your cybersecurity operations. It does this by bringing together a wide array of security technologies under one roof, making your life way less complex.
2. Automated Response
XDR also helps businesses with automated threat response capabilities. It is all about cutting down the time it takes to neutralize the threats, and helping businesses deal with cyber threats “in the blink of an eye.”
3. Holistic Threat Visibility
XDR comes up with an “all-seeing” eye in the cybersecurity realm. It covers every “nook and cranny” of your IT infrastructure. This means that no threat goes un-noticed, no matter where it rears its ugly head. This visibility across your IT landscape slashes any blind spots in your IT infrastructure, and substantially improves your threat detection game.
4. Faster Investigations Boost Enterprise Productivity
With XDR, your security teams can work more efficiently. It helps businesses prioritize threats, and reduce the number of false alarms by using intelligent analytics and automations. This means your teams can focus more on the most critical threat events, and use automation to handle known or repeat incidents.
Conclusion
In a world where cyber threats continue to evolve, XDR is a giant leap forward. And the evolution from Endpoint Detection and Response (EDR) to Extended Detection and Response (XDR) is a testament to the ongoing advancements in cybersecurity
It is high time businesses take the leap towards the all-encompassing threat visibility, detection and response capabilities of XDR, and equip their critical IT operations with the comprehensive protection they deserve.
But how can you seamlessly transition to XDR and harness its full potential for your enterprise? That’s where ATSG comes in. Our Managed IT Services and Intelligent Technology Solutions are designed to provide you with peace of mind.
ATSG’s team of highly experienced and certified professionals is well-versed in the intricacies of designing, implementing and managing XDR for you. We offer varying degrees of XDR, ranging from just design and implement, to the full service stack, which not only involves the design and implementation part, but also includes effective management of the XDR solution for your enterprise.
Don’t just settle for good enough cybersecurity – choose excellence instead. ATSG is your trusted partner in ensuring that your organization remains resilient against today’s complex cyber threats.
Contact ATSG for industry leading Cybersecurity, Managed IT, Technology and Cloud Computing solutions for your enterprise.




