Organizations are becoming more vulnerable to cyber threats globally, with constantly increasing reliance on computers, networks, programs, and data. It is not enough to rely on traditional IT professionals and legacy security controls for protection. There is a requirement for threat-intelligence tools and holistic security programs, to reduce organizations’ cyber risk and highlight potential attacks.
Understanding the requirement to build a strong cybersecurity system has become indispensable for an organization and its resources.

The Challenge of Discovering Cybersecurity Threats
Cyber threats originate from various actors, including corporate spies, hackers, terrorist criminals, etc. In recent years, numerous high-profile cyber attacks have resulted in exposing sensitive data. In most of these attacks, the cyber security threat was enabled by the organization’s failure to implement and safeguard sensitive data and networks. Cyber attackers can use individual information or a company’s sensitive data to potentially damage the organization. This is why organizations need to invest in strong cybersecurity professionals and systems.
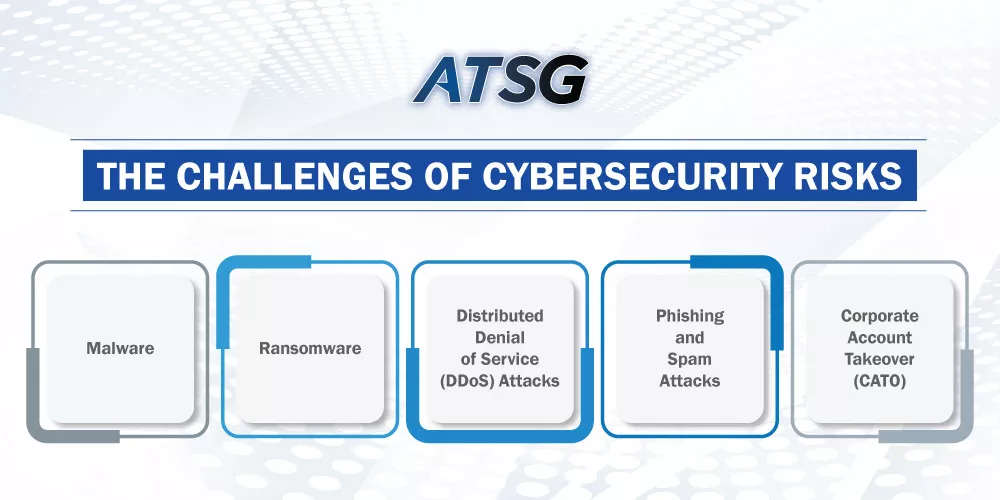
The Challenges of Cybersecurity Risks
Cybersecurity is a real problem that is faced by almost everyone with a device. Without comprehensive IT security management, organizations tend to face financial, legal, and reputational risks. There are plenty of common security risks which are identifiable and preventable. Following is a list of some widely prevalent, and highly repetitive cybersecurity threats that enterprises need to be watchful of.
Malware:-
It is one of the most prolific and common forms of security threats. It is activated through malicious software installing itself via emailing a link, or an attachment to the user, causing unusual behavior. Organizations can prevent this by introducing the latest anti-malware programs, and spreading employee awareness about suspicious items. In a lot of cases, the perpetrator of a malware attack tries to impersonate/mask either someone from within your organization or anyone close to you.
Ransomware:-
It is a variant of malware, which installs itself on the user’s system or network. It prevents normal functionality, by gaining unauthorized access to your data and encrypting it. As a result, the access of even legitimate users to their data is denied, until a ransom has been paid to the perpetrator. It is vital to keep updating anti-viruses and avoiding malicious links to prevent the possibility of an attack. Backing up and replicating information is key to keeping ransomware attacks from becoming disastrous. With an effective backup strategy in place, an organization can avert the possibility of paying the ransom, as data can be restored from the repository instead.
Distributed Denial of Service (DDoS) Attacks:-
DDoS is an attack vector in which malicious parties target servers and networks, overloading or overwhelming them with traffic. This affects the operations and processes of the server or network, often disabling the system. To prevent such attacks, organizations need to identify the malicious traffic and IPs that are linked to such attacks. Such attacks often require servers to be taken offline and managed for maintenance. For the affected organization, this means downtime, which not only results in financial losses but reputational damage as well.
Phishing and Spam Attacks:-
These are one of the oldest attack vectors and rely heavily on social engineering to perpetrate the attack. Phishing emails and messages take sensitive data from the users and misuse it against the individual or the organization. In this case, organizations need to train and secure their users by providing them with the ability to identify the telltale signs of such messages or emails.
Corporate Account Takeover (CATO):-
This is a corporate attack that impersonates the organization to authorize financial transactions and wire transfers. The funds are sent to accounts held by cyber criminals, which leads to businesses becoming even more vulnerable to other attacks. This form of crime can be prevented by educating the users, and evolving a comprehensive, multi-tier mechanism for the dispersal of corporate funds. Adopting the CATO best practices document, in true letter and spirit, can establish a blueprint for safeguarding financial transactions by organizations.
How to Effectively Prevent Cyber Attacks?
Cybersecurity is indeed a huge and multi-dimensional challenge for organizations. In a lot of cases, organizations lack the in-house capacity to develop strong cyber security mechanisms and controls. In such a case, leveraging the expertise and tools of an organization, such as ATSG, which specializes in cyber security, can help an organization handle and avoid the possibility of a cyber-attack.
Conclusively, these types of cyber risks continue to grow in complexity. Understanding them can lead to the best way, to defend the organization. Simpler forms of attacks, such as malware and phishing, are by far the most detrimental. Understanding the methodologies of attackers beforehand, and being well-prepared can mitigate the imminent threats posed by them. By adopting the latest cyber security trends and new technologies via ATSG, enterprises can really put themselves one step ahead of the looming cyber threats out there.




